Business Email Compromise is now one of the top threats faced by businesses of all sizes, across every vertical. Threat actors often go unnoticed for months inside mailboxes while they plan their attacks on your business and customers, downloading files and sending false emails.
These bad guys are often after money or in some cases revenge, and by using mailbox rule changes to remain unnoticed, attackers can cause significant damage to individuals and the reputations of organisations.
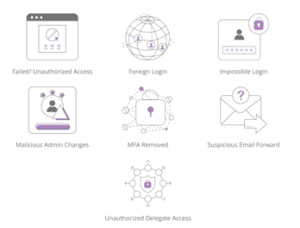
It is now generally accepted that the time it takes to detect and respond to a business email compromise incident often determines the size and the scale of the damage. With technology becoming more advanced, your staff and data can be a lot more vulnerable to cyber-attacks (click image below to expand).
It’s important that you protect your information within Office 365 and keep it secure. To mitigate these risks, businesses must now ensure they have processes in place that will:
- Get insight into threat management and file integrity monitoring to prevent leakage or tampering of Microsoft office 365 data.
- Detect unauthorized access attempts to Microsoft Office cloud mailboxes, folders, calendars and contacts.
- Detect data mobility with audit logging and build custom alerts.
- Track admin activity and changes to the O365 tenant.
- Track email delegate activity including the movement and deletion of data.
- Monitor geolocation access with IP location sourcing, tracking where people are accessing company data from.
- Prevent data hijacking by monitoring email forwarding rules.
- Detect changes to MFA and failed logins.
- Track brute force login attempts.
- Detect anomalous mass file downloads.
- Detect impossible logins from different geolocations for example users trying to login from Russia one minute, then Vietnam the next.
Tycom Ubiquity Office 365 Security Monitoring is a managed security service bolt on that collects, aggregates, and normalizes log data from your Microsoft Office 365 tenant using an Artificial Intelligence analytics platform, SIEM Threat Intelligence, and is monitored 24/7 365 days a year by a dedicated Security Operations Centre (SOC).
In the event of a potential Office 365 security breach, our team will immediately alert you and take steps to protect your company data. The primary goal of the 365 SOC service is to protect your business from Business Email Compromise and identify threat like behaviour within your Office 365 environment like unauthorized access to cloud mailboxes, admin changes in the environment, impossible logins, mass file downloads, and brute force attacks.
Remember when your cloud account is breached, traditional anti-virus solutions or internal solutions like firewalls won’t be triggered. Our next gen AI based Microsoft 365 cloud monitoring solution can be activated quickly to provide this level of protection to your business to ensure you are keeping pace with the Cyber Criminals.